IronWiFi RadSec Secure Radius Servers
RadSec General Information
RadSec or Radius over TLS is an extension to the RADIUS protocol, that uses secure tunnels estabilished between the Radius Client and Radius Server to encapsulate Authentication, Authorization, and Accounting (AAA) protocol messages. Connection is authenticated using Client Certificates. Without the correct client certificate, issued by our Secure PKI Infrastructure, RadSec server will not even allow the tunnel to be estabilished. Each client certificate is issued for the specific customer, region and network, making it impossible for the unauthorised radius client to connect or to intercept the messages.
How to enable RadSec on your network
Thanks to your Modern and Secure PKI Infrastructure enabling RadSec servers in your network and obtaining the Certificate Pack is very straightforward.
- Sign in to the IronWiFi Management Console
- Go to Networks -> Select the network you want to enable the RadSec for.
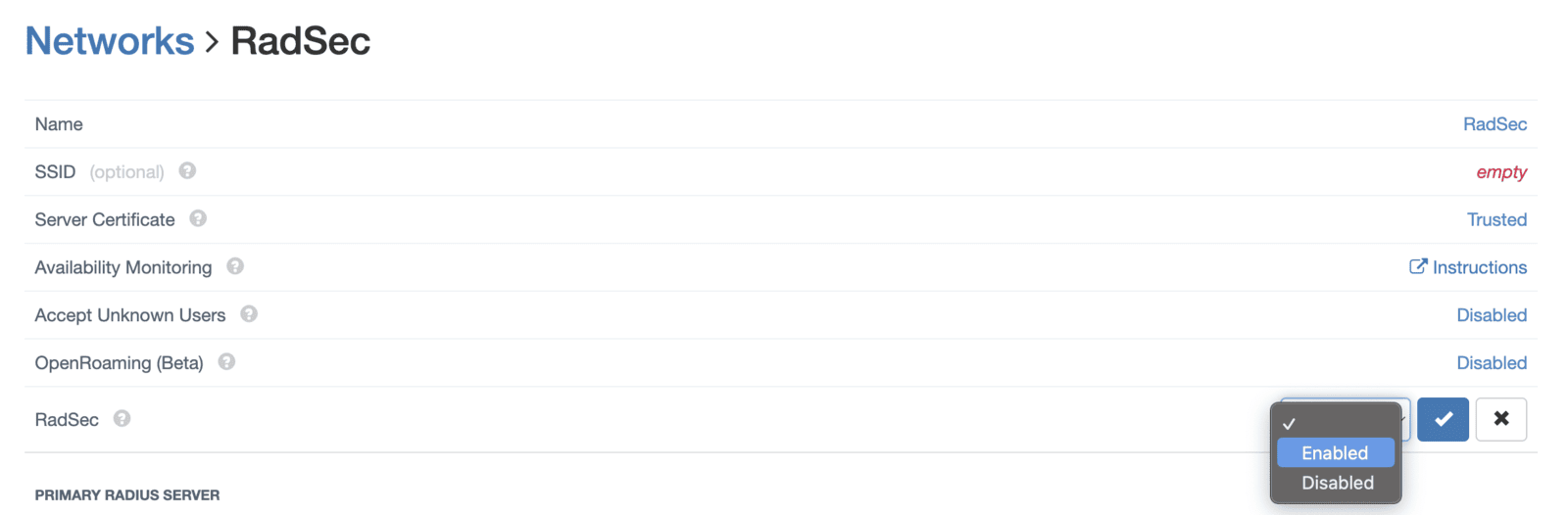
- Select Enabled from the drop-down menu
- The page will reload and you will see the link to the certificate bundle, consisting of the Root CA certificate, the RadSec Signing Intermediate CA certificate, your Client Certificate and the Client Key. You need to upload them to your controller, and set up the IP address and port, with the standard RadSec secret: 'radsec', and you should be up and running !
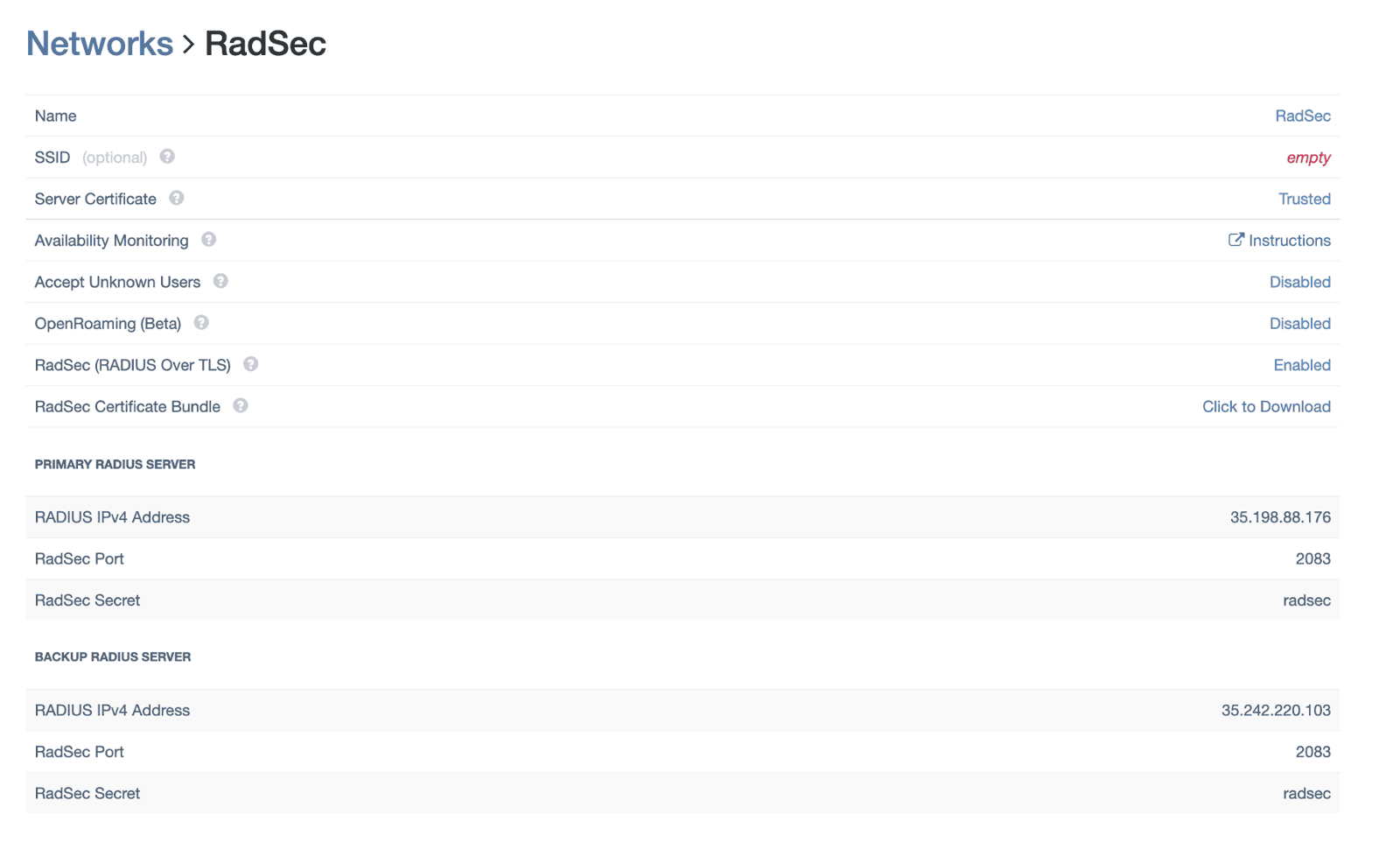
- You should use the same details for Authentication and Accounting, RadSec server automatically distinguishes between the two and directs the requests and updates to the correct internal destinaton.
Related Articles
IronWiFi RadSec Secure Radius Servers
RadSec General Information RadSec or Radius over TLS is an extension to the RADIUS protocol, that uses secure tunnels estabilished between the Radius Client and Radius Server to encapsulate Authentication, Authorization, and Accounting (AAA) protocol ...IronWiFi PKI Infrastructure
The old Root CA certificate has expired on May 18, 2024. You can download the new certificates below. Hardware-Backed Security IronWiFi PKI infrastructure employs the latest industry standards for the private key protection, relying on the HSM ...IronWiFi PKI Infrastructure
The old Root CA certificate has expired on May 18, 2024. You can download the new certificates below. Hardware-Backed Security IronWiFi PKI infrastructure employs the latest industry standards for the private key protection, relying on the HSM ...Juniper Mist HS2.0 / Passpoint with RadSec
Prerequisites Access to the Mist Dashboard as a user with administrative privileges. Access to the IronWiFi Management Console - Sign in or Open Account RadSec enabled on your Network as detailed here (you will need to download the certificate ...MikroTik ROS v7 OpenRoaming with RadSec
Sign in to the IronWiFi Management Console Go to Networks -> Select the network you want to enable the OpenRoaming and RadSec for. Select Enabled from the drop-down menu for both RadSec and OpenRoaming The page will reload and you will see the link ...