Intune - TTLS-PAP with IronWiFi PKI
This is a guide for setting up TTLS-PAP with IronWiFi's multi-tiered HSM based Certificate Authority and Microsoft Intune to provision Windows OS based devices, using user profile.
What do you need ?
-
IronWiFi Root CA Certificate - certificate of the IronWiFi Root Certificate Authority - iw-rsa-root-ca.cert.crt. The file can be downloaded from this link
- IronWiFi Intermediate Certificate - certificate of the IronWiFi Intermediate Certificate Authority signing the CSR requests - iw-rsa-intermediate-ca.cert.crt. The file can be downloaded from this link
1. Sign in to the Microsoft Intune management console
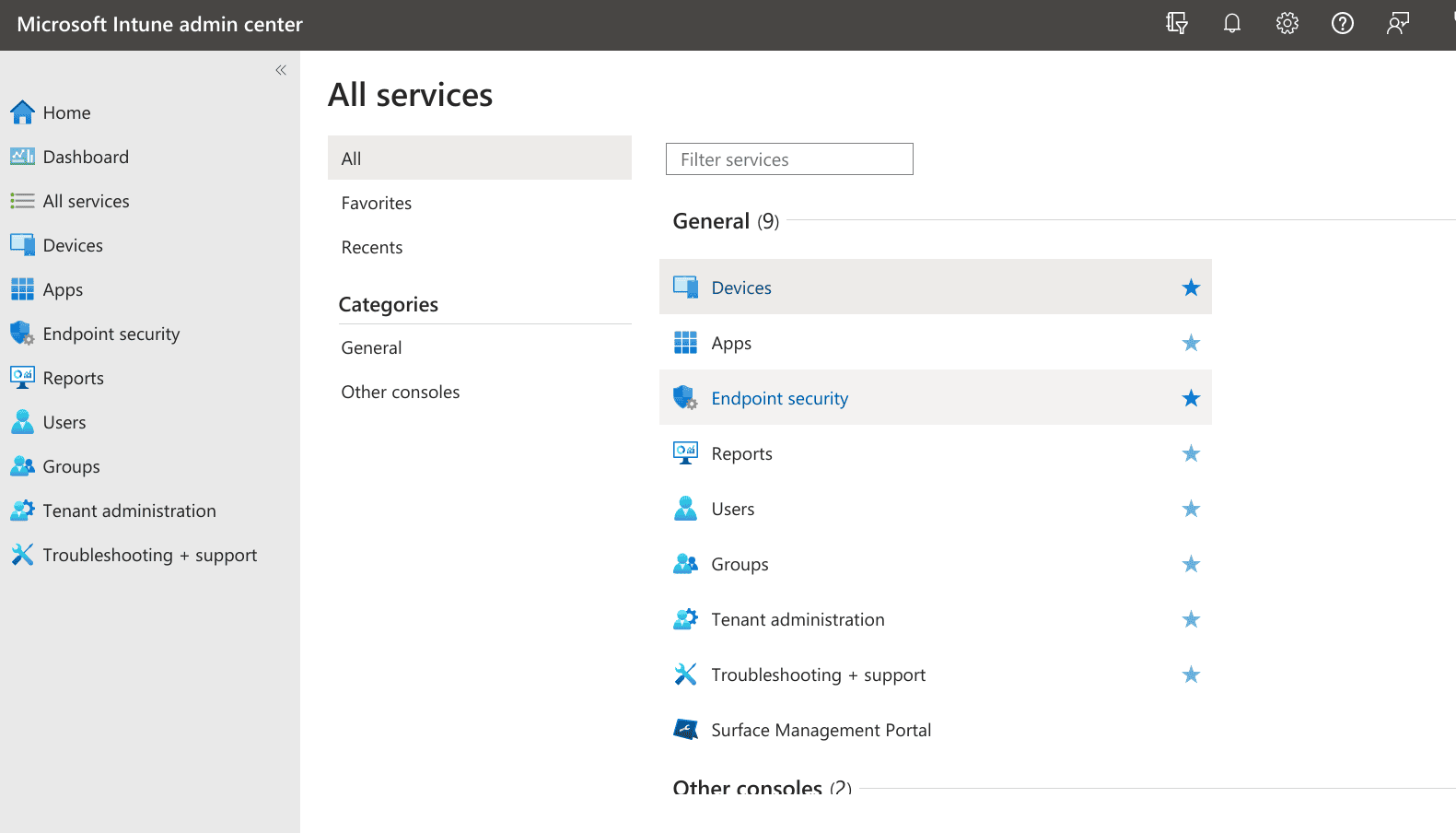
2. Navigate to Devices > Windows > Configuration Profiles
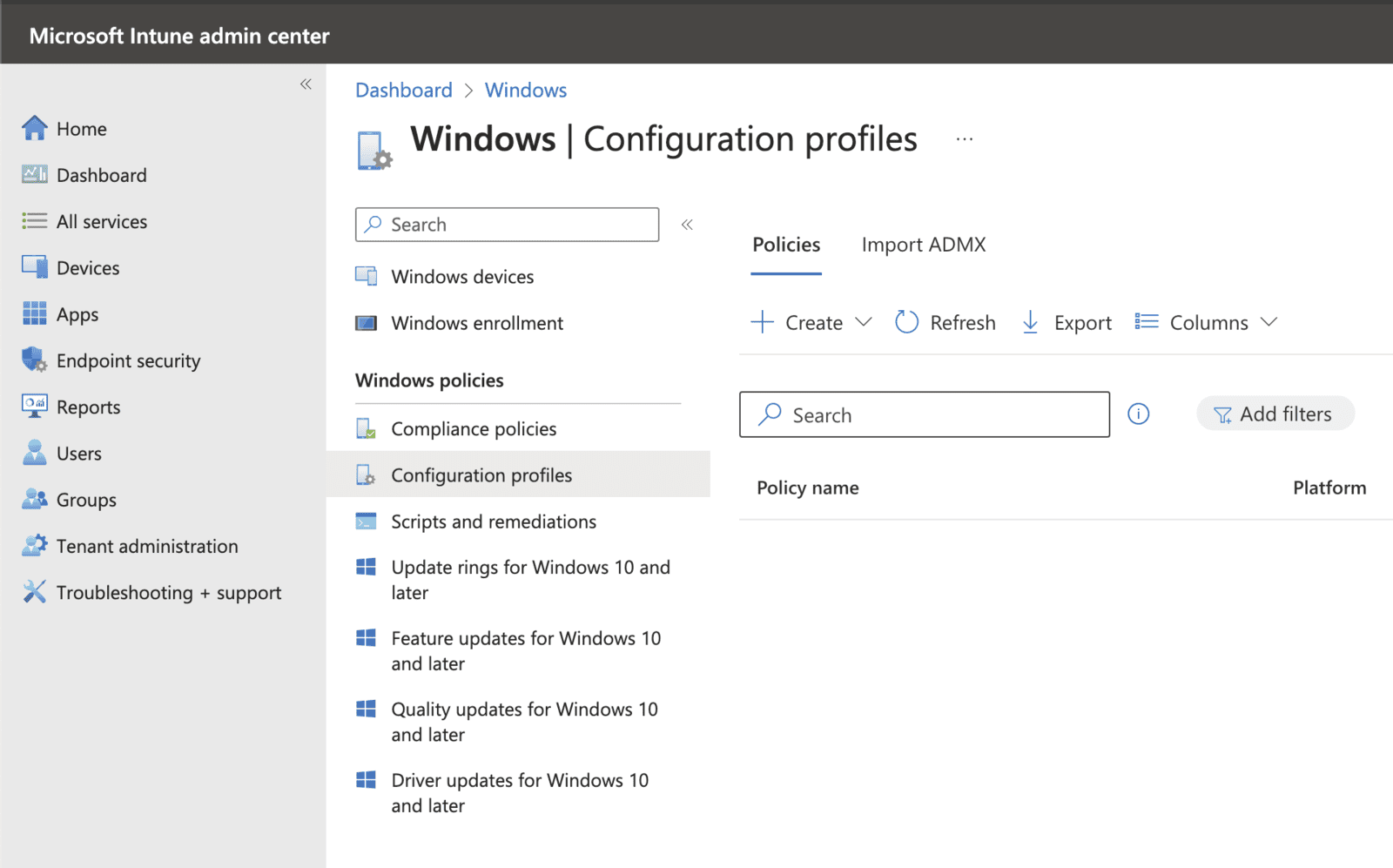
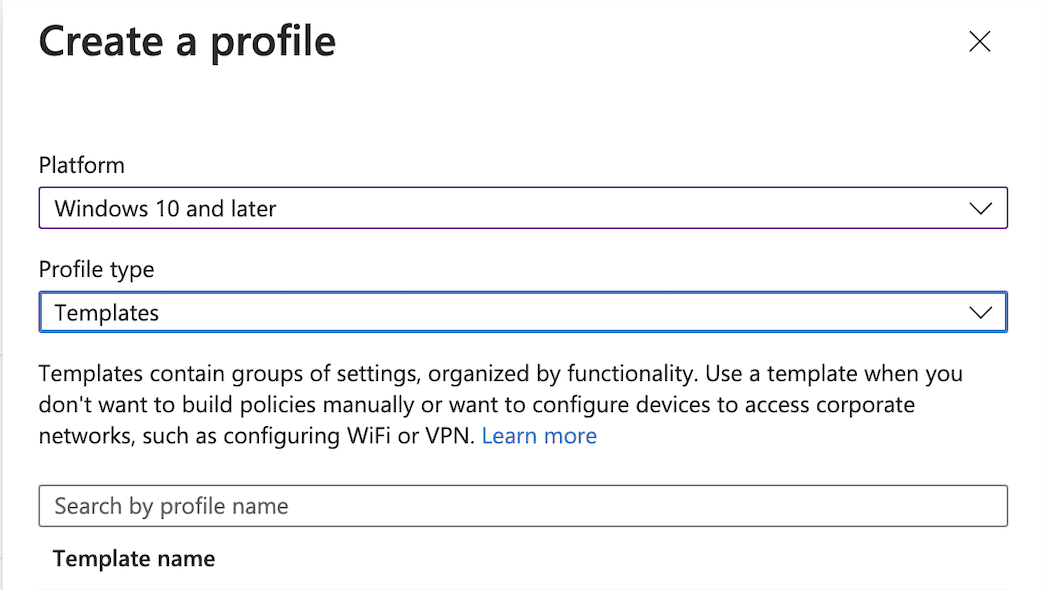
3. Click Create > New Policy and choose the Platform: Windows 10 and later, Profile type: Templates and search for Trusted Certificate template
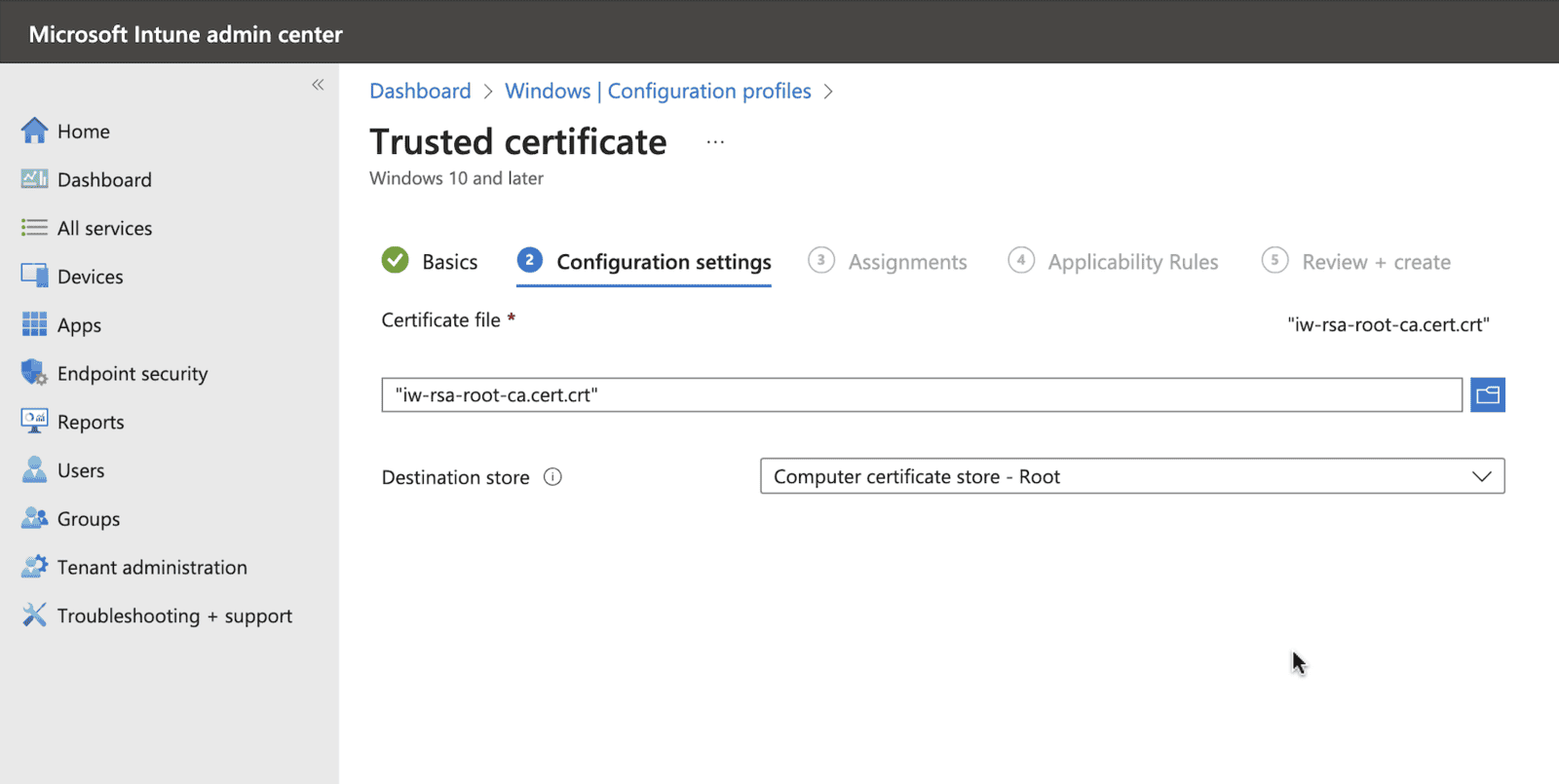
4. Add the certificate with the following configuration settings:
- Name - IW TTLS Root CA
- Certificate file - iw-rsa-root-ca.cert.crt downloaded from the link above.
- Destination store - Computer certificate store - Root
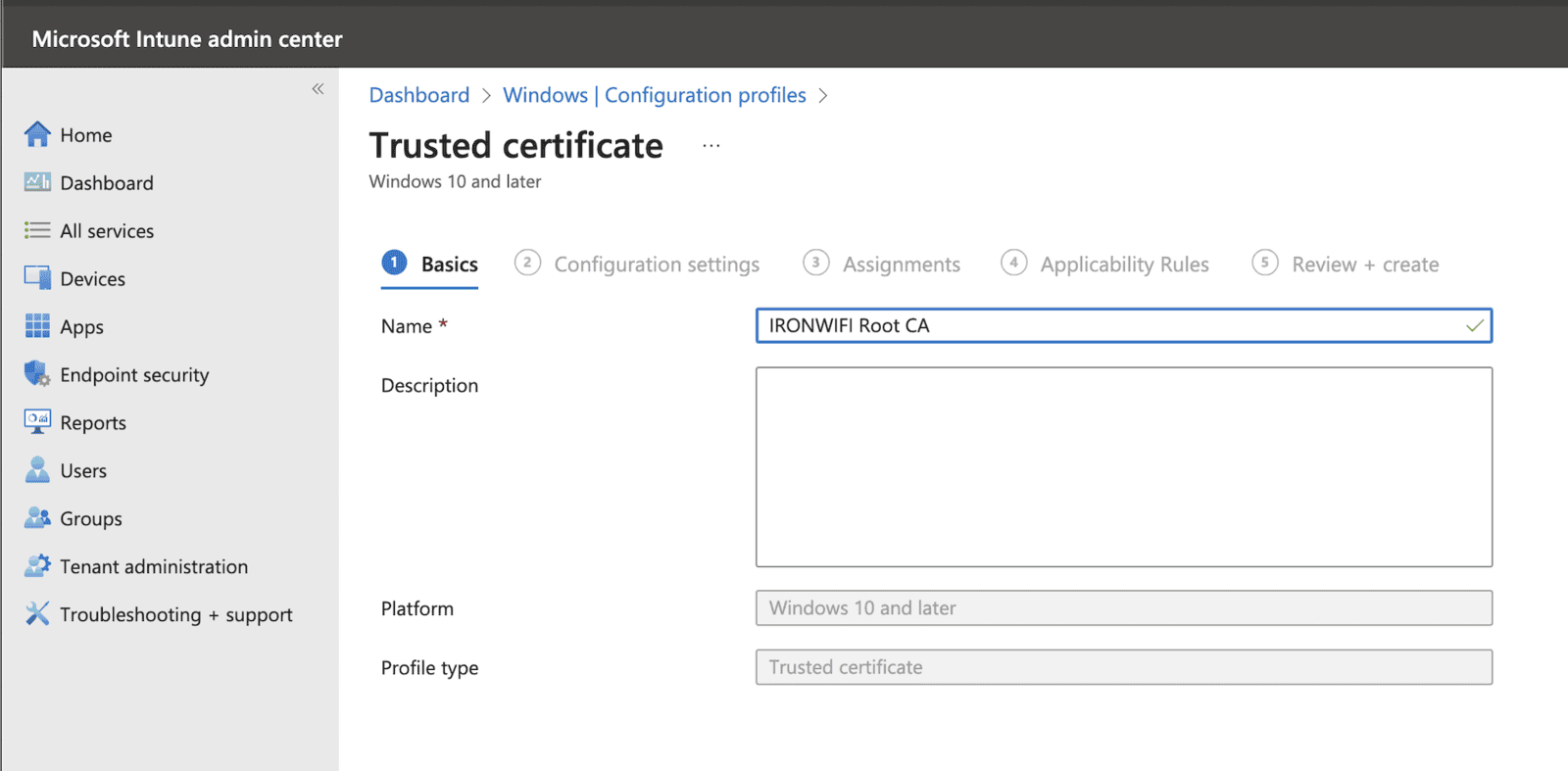
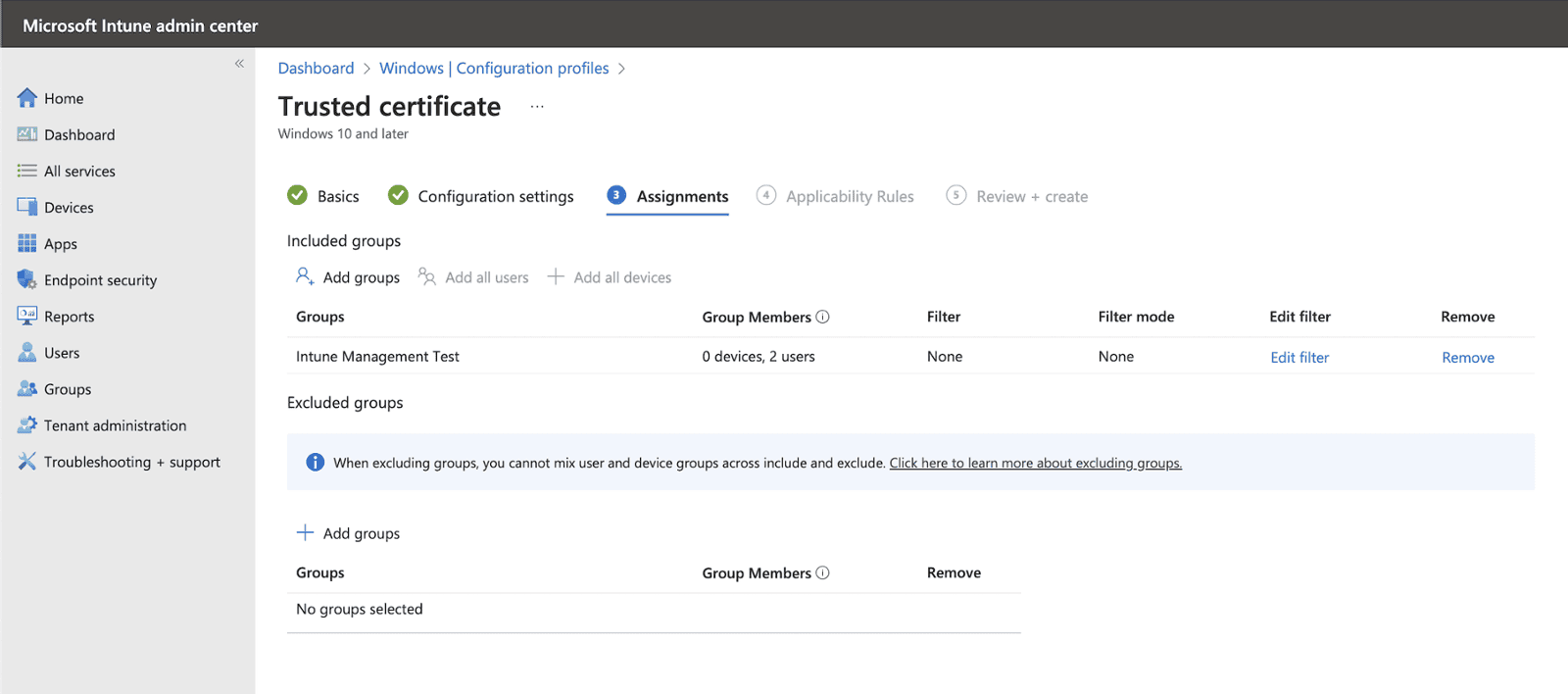
5. Select correct Assignments and Applicability Rules:
!NOTE! Make sure that you are using USER based assignments for all profiles.
6. Review and create the profile
7. Create another Configuration Profile for Trusted certificate repeating the steps from step 4 with following configuration settings:
- Name - IW TTLS Intermediate CA
- Certificate file - iw-rsa-intermediate-ca.cert.crt downloaded from the link above.
- Destination store - Computer certificate store - Intermediate
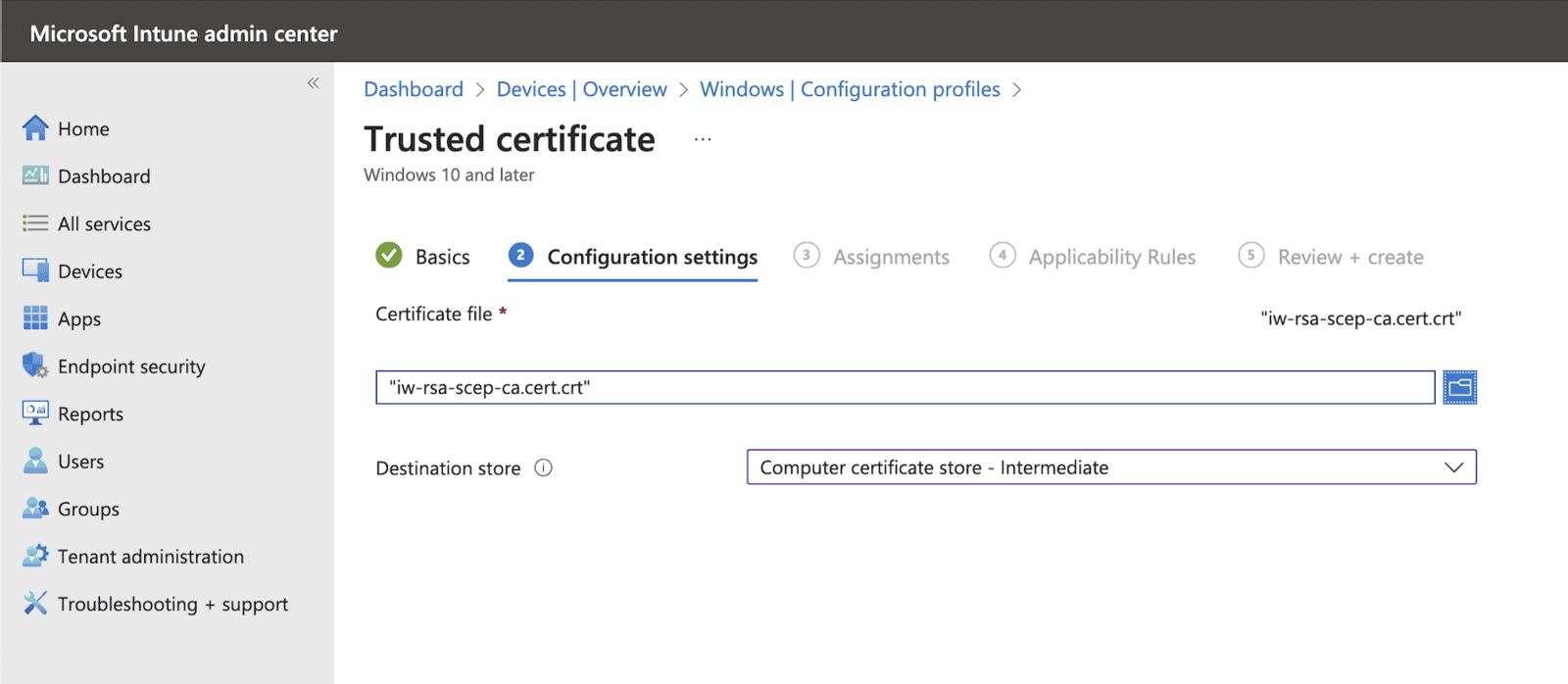
8. Select correct Assignments and Applicability Rules and review and create the profile as you have done when adding Root CA
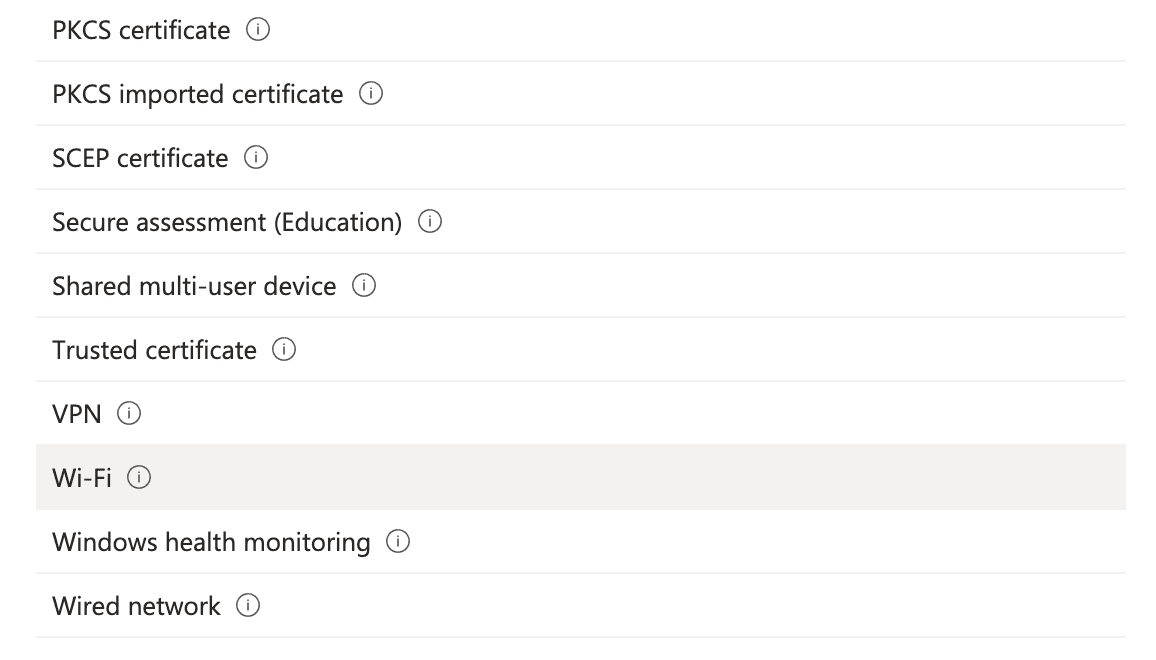
9. Create Configuration Profile for WiFi using steps from step 4, this time selecting Wi-Fi template:
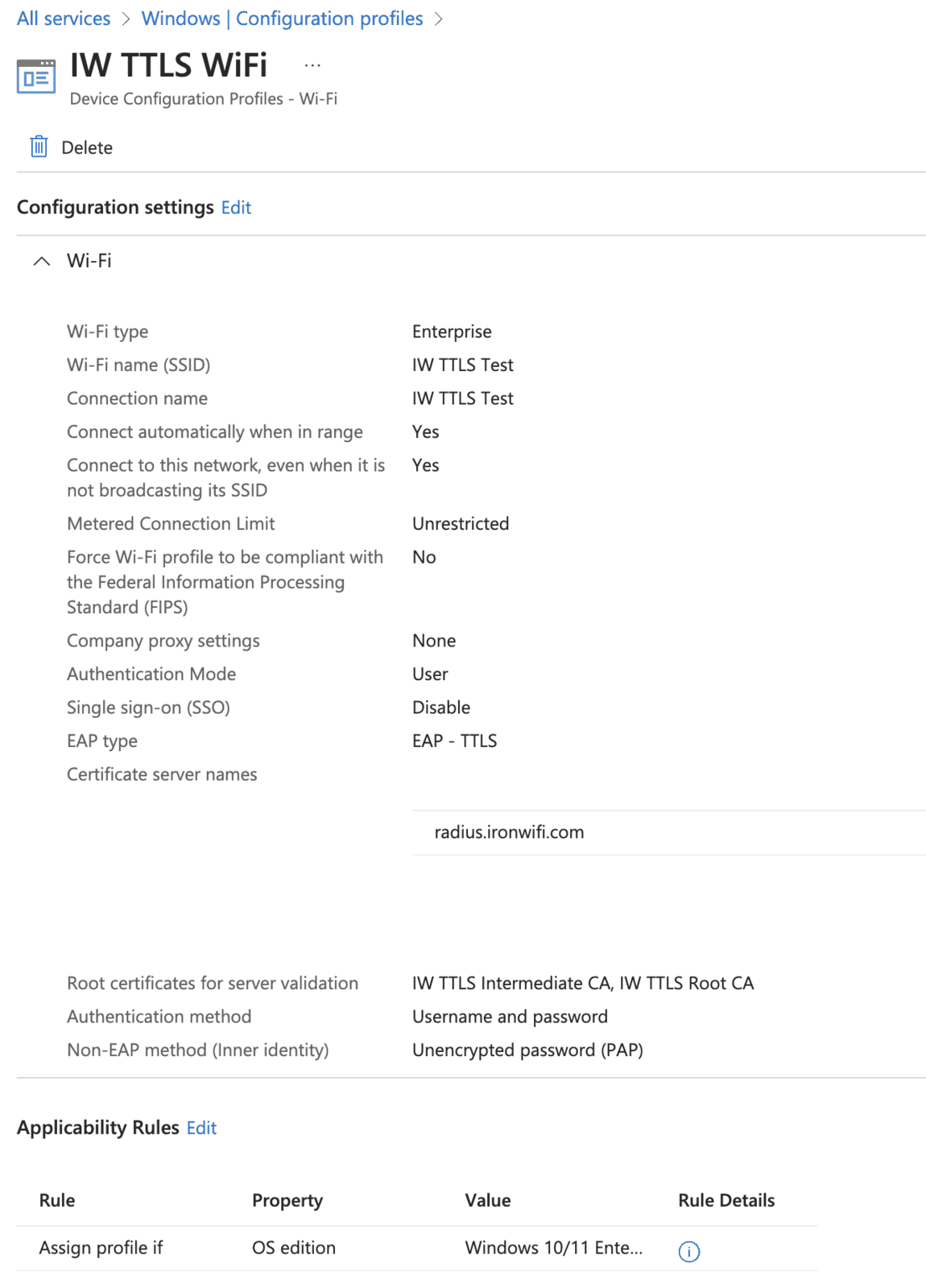
14. Select type: Enterprise and use the following settings:
- Wi-Fi name - Your SSID
- Connection name - Your connection name
- Connect automatically when in range - Yes
- Connect to more preferred network if available - No
- Connect to this network, even when it is not broadcasting its SSID - Yes
- Metered Connection Limit - Unrestricted
- Authentication Mode - User
- Single sign-on (SSO) - Disable
- EAP type - EAP - TTLS
- Certificate server names - radius.ironwifi.com
- Root certificates for server validation - The trusted certificates created in previous steps - IW TTLS Intermediate CA, IW TTLS Root CA
- Authentication method - Username and password
-
Non-EAP method (Inner identity) - Unencrypted password (PAP)
Related Articles
Linux - TTLS + PAP
How to Connect to Wi-Fi Using TTLS + PAP on Linux TTLS + PAP is a secure Wi-Fi authentication method used in enterprise and academic networks. This guide covers how to connect using both graphical tools and the command line on a Linux system. Option ...Android – TTLS + PAP
How to Connect to Wi-Fi Using TTLS + PAP on Android TTLS + PAP is a common enterprise-level Wi-Fi authentication method. This guide explains how to connect to such a network using an Android device. Step-by-Step Instructions Open your Android ...Chromebook OS – TTLS + PAP
How to Connect to Wi-Fi Using TTLS + PAP on Chromebook TTLS + PAP is a secure Wi-Fi authentication method that tunnels credentials inside a TLS connection. Chromebooks support this configuration natively, making it suitable for enterprise and campus ...SCEP with Intune - IronWiFi PKI - User Auth
The Simple Certificate Enrollment Protocol (SCEP) is a protocol that allows devices to easily enroll for a certificate by using a URL and a shared secret to communicate with a PKI. This is a guide for setting up SCEP with IronWiFi's new multi-tiered ...SCEP with Intune - IronWiFi PKI - Device Auth
The Simple Certificate Enrollment Protocol (SCEP) is a protocol that allows devices to easily enroll for a certificate by using a URL and a shared secret to communicate with a PKI. This is a guide for setting up SCEP with IronWiFi's new multi-tiered ...