Azure AD SAML
This page provides instructions on how to configure your Azure Active Directory to allow Captive Portal authentication with SAML.
- Navigate to https://portal.azure.com
- Go to the Azure Active Directory submenu
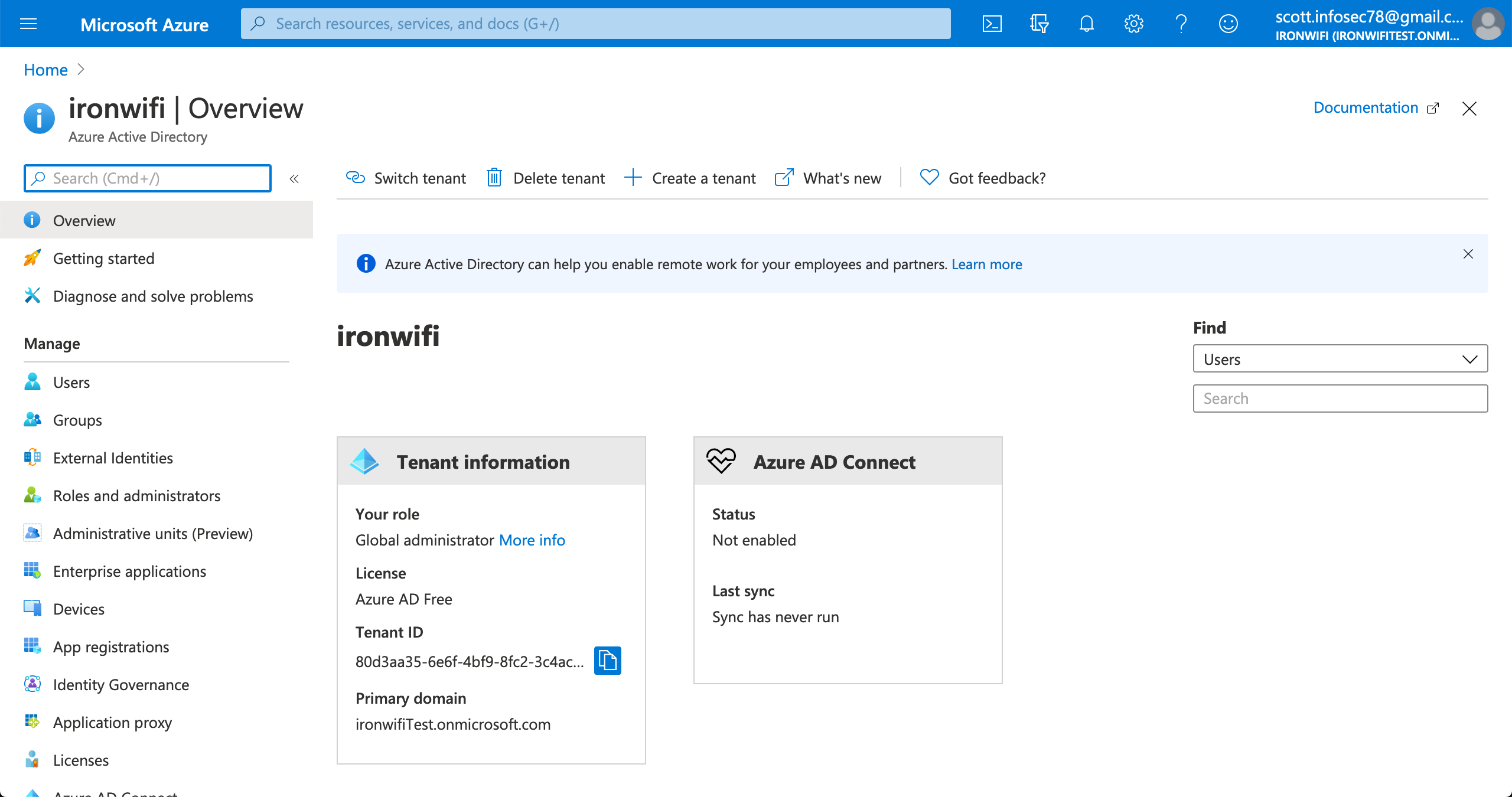
3. Select the active directory you wish to use for SSO
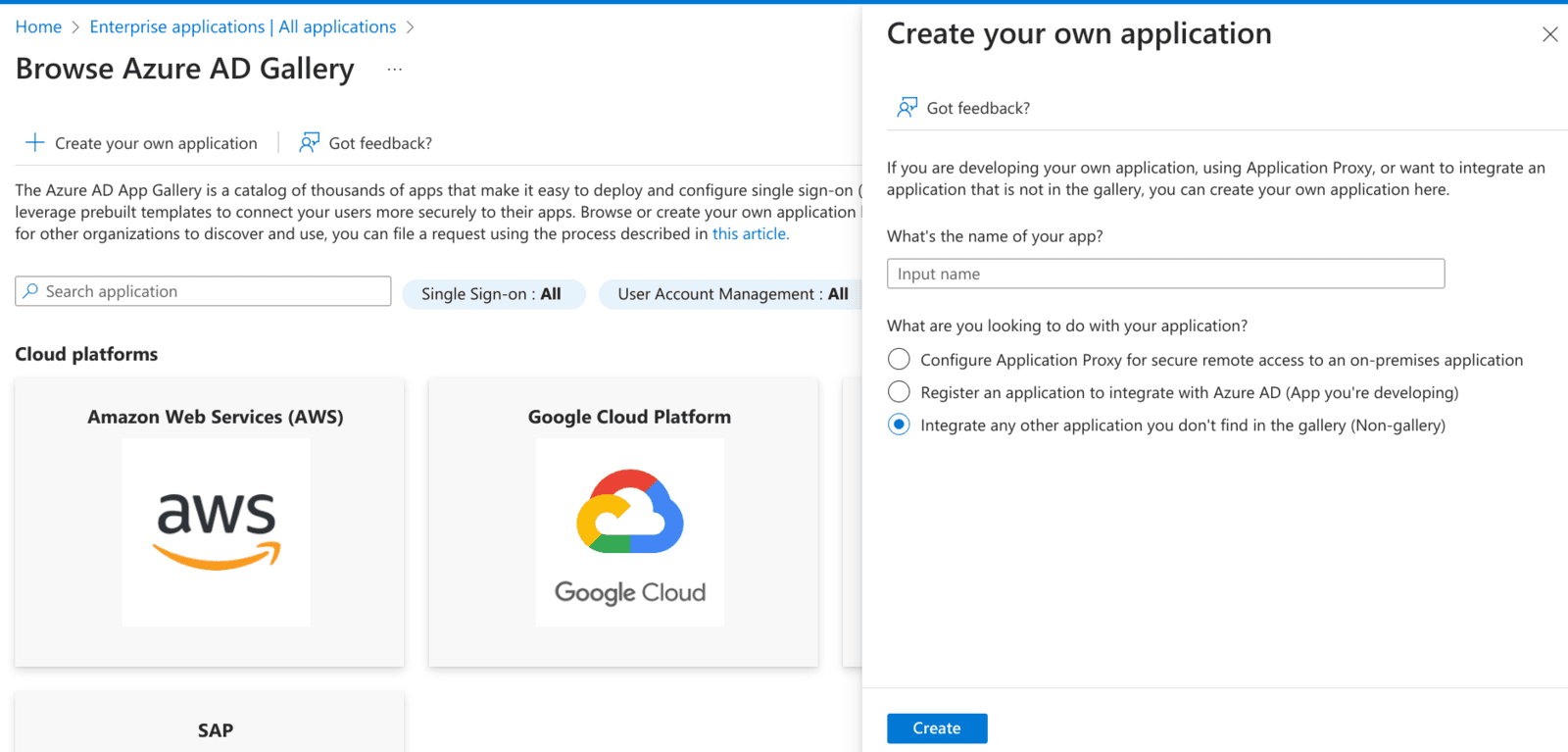
4. Click on Enterprise applications > New application > Create your own application(non-gallery)
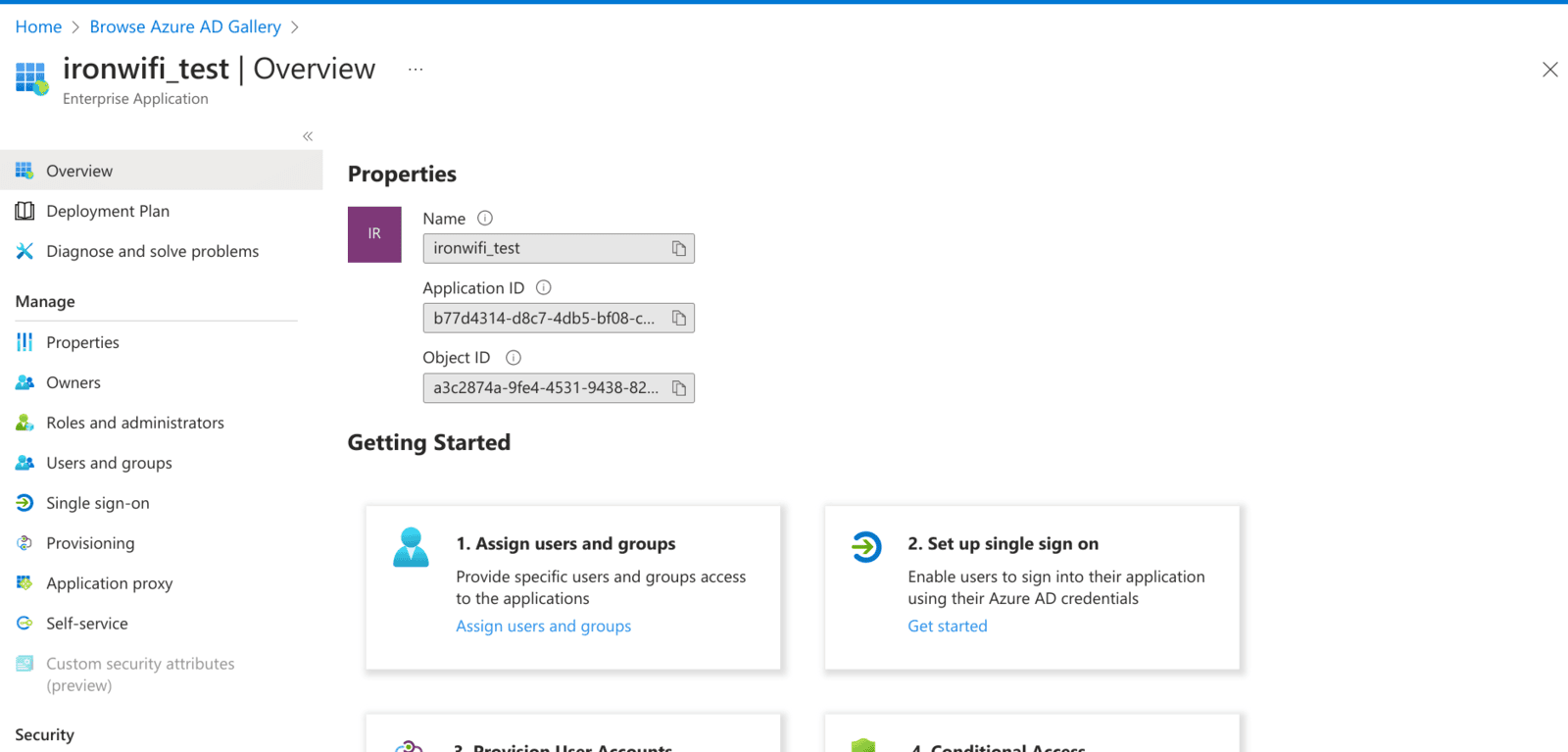
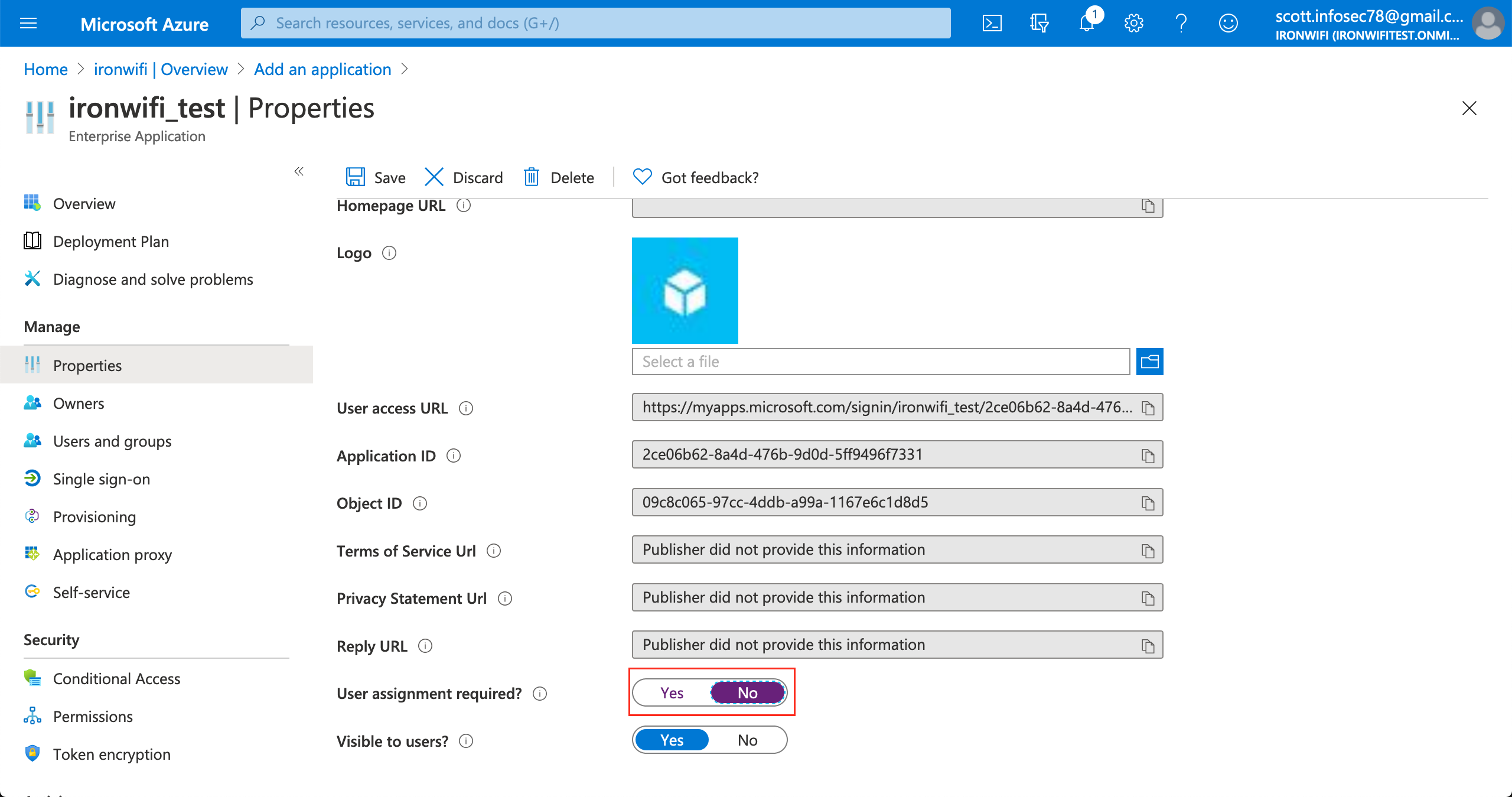
6. In the application settings page, click on Properties
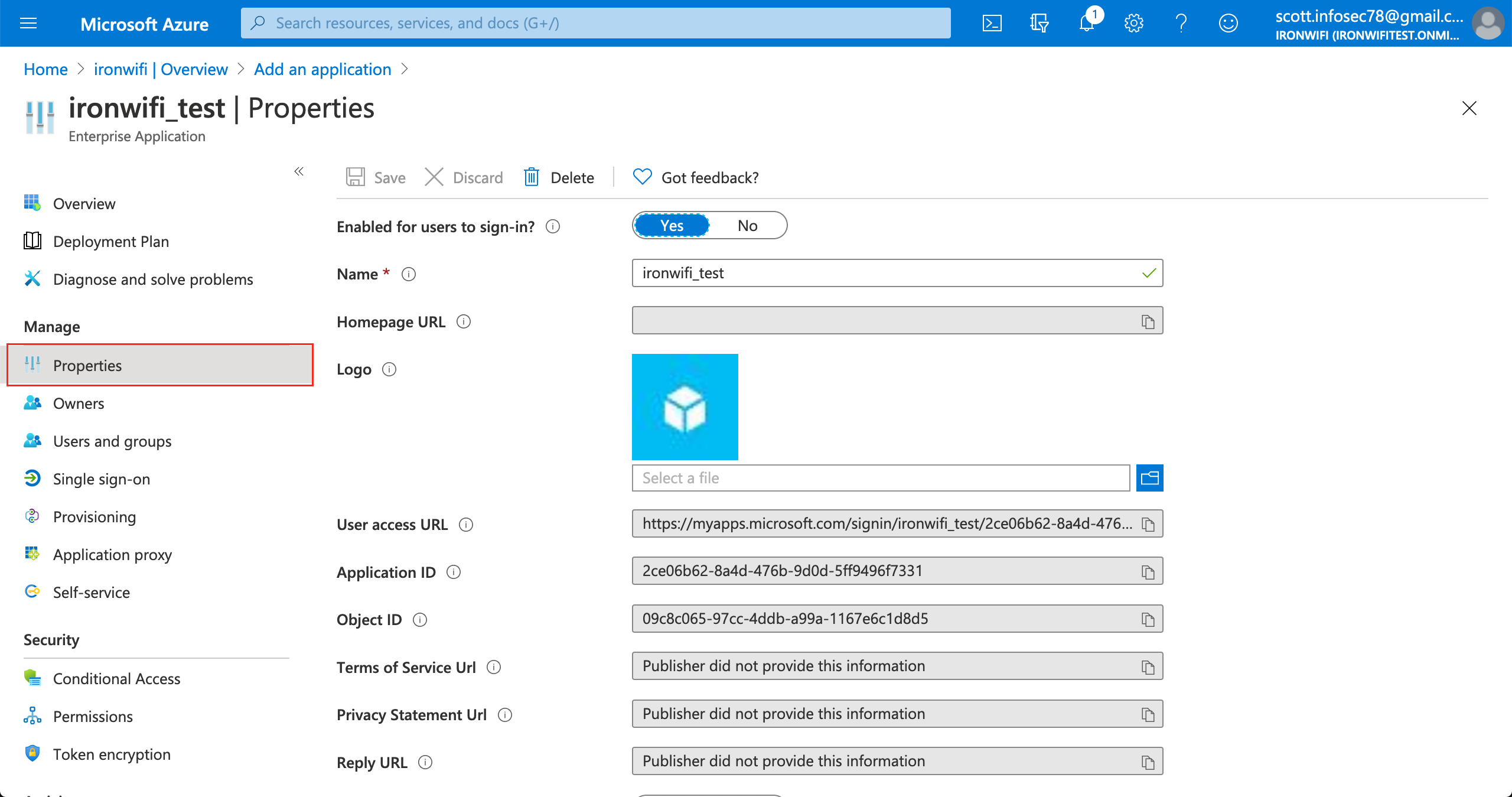
7. Change "Assignment required" value to No
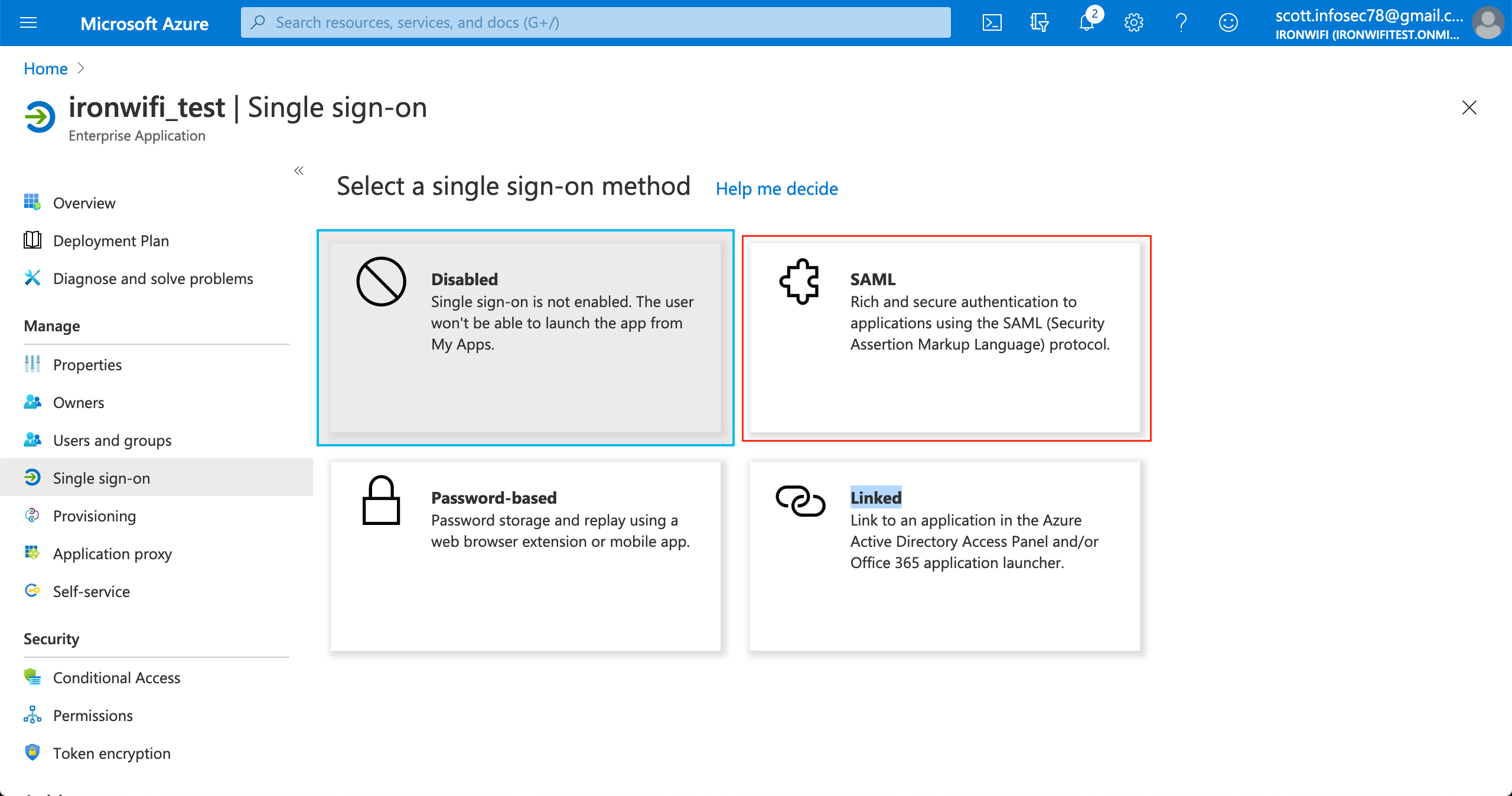
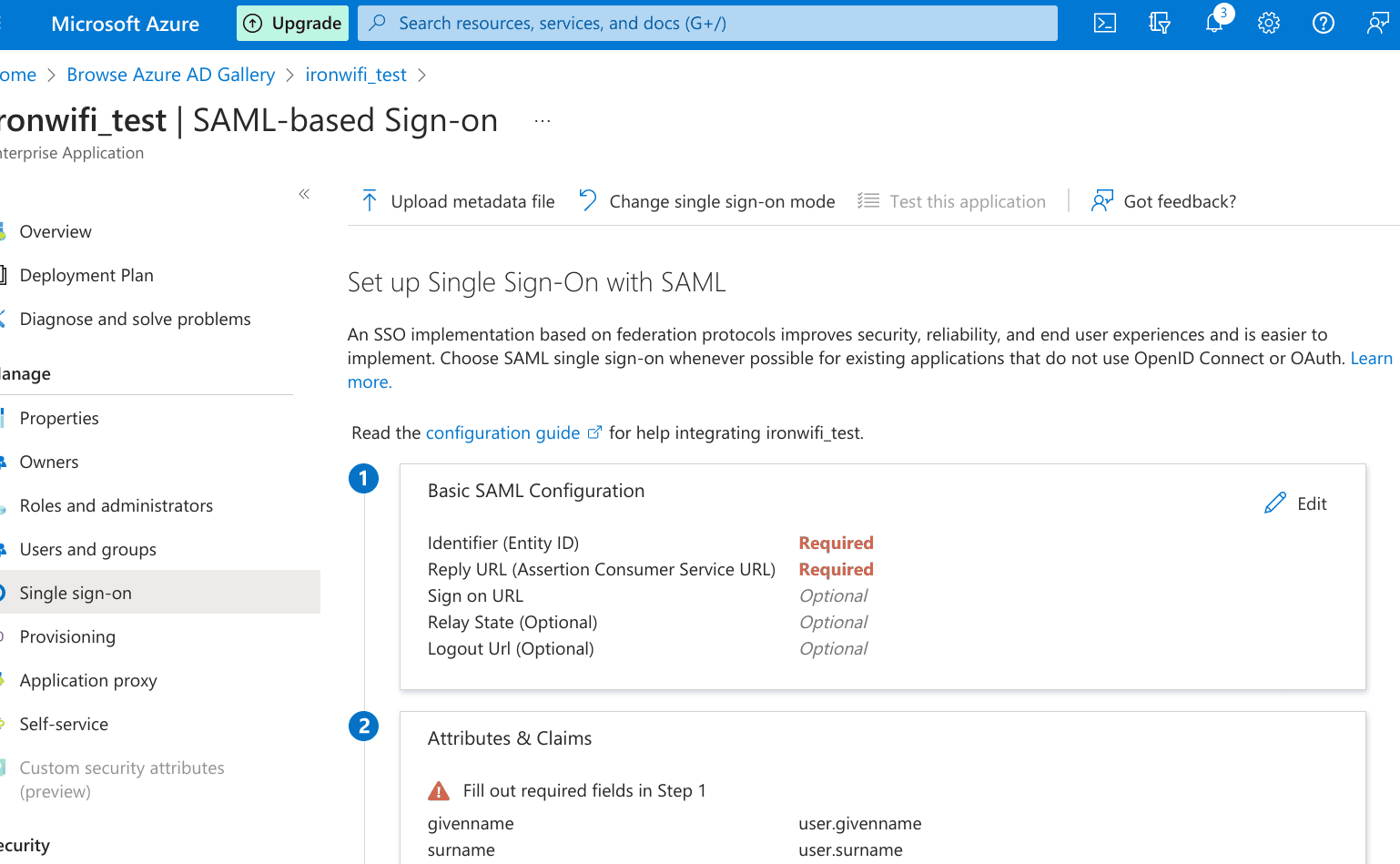
9. Enter Identifier (Entity-ID) and Reply URL.
Valid values are displayed in IronWiFi Console > Captive Portal settings>Authentication Providers.
Sample values: Entity ID - https://europe-west2.ironwifi.com/api/signin/saml2
Reply URL - https://europe-west2.ironwifi.com/api/signin/saml2?acs
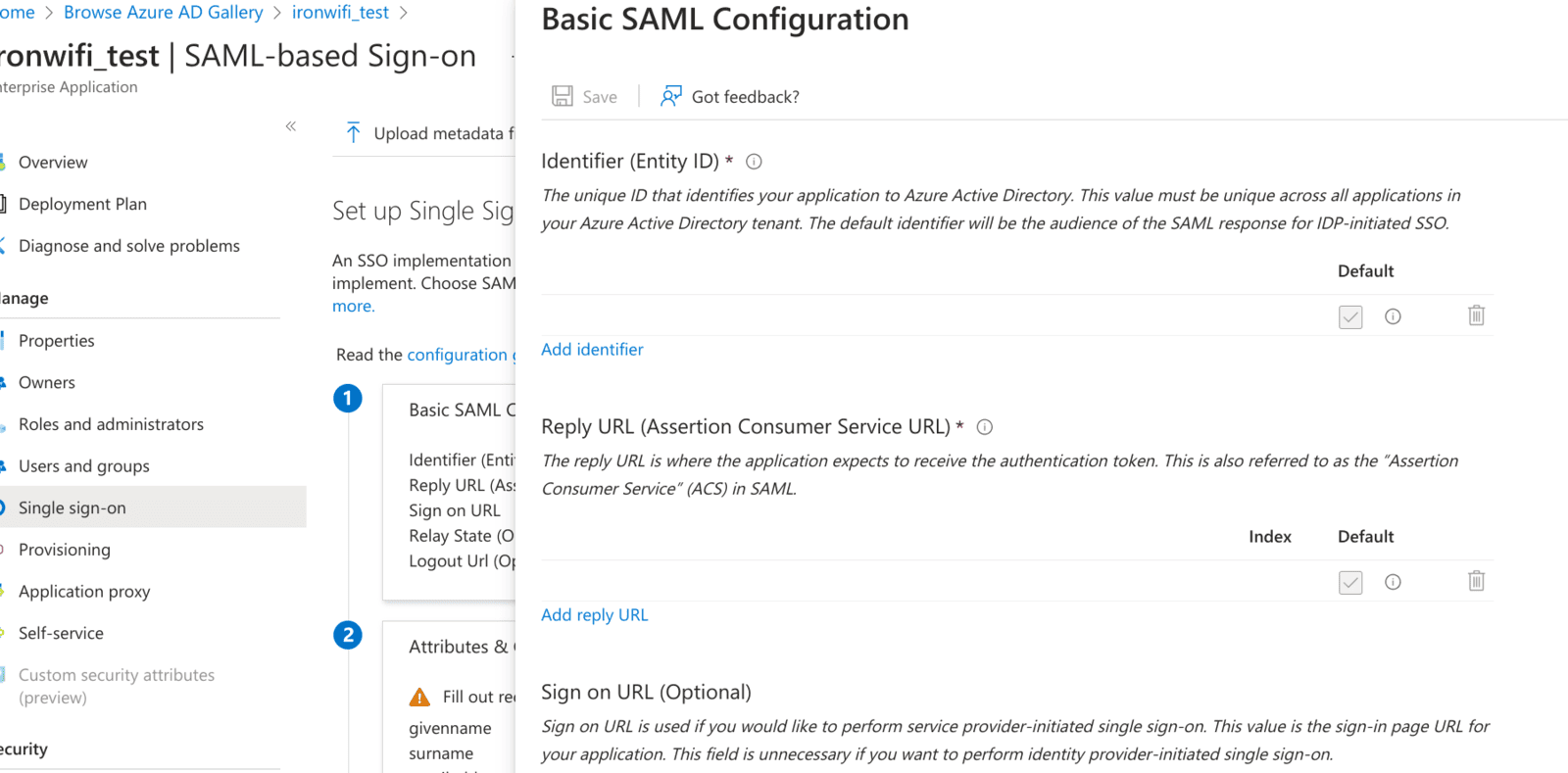
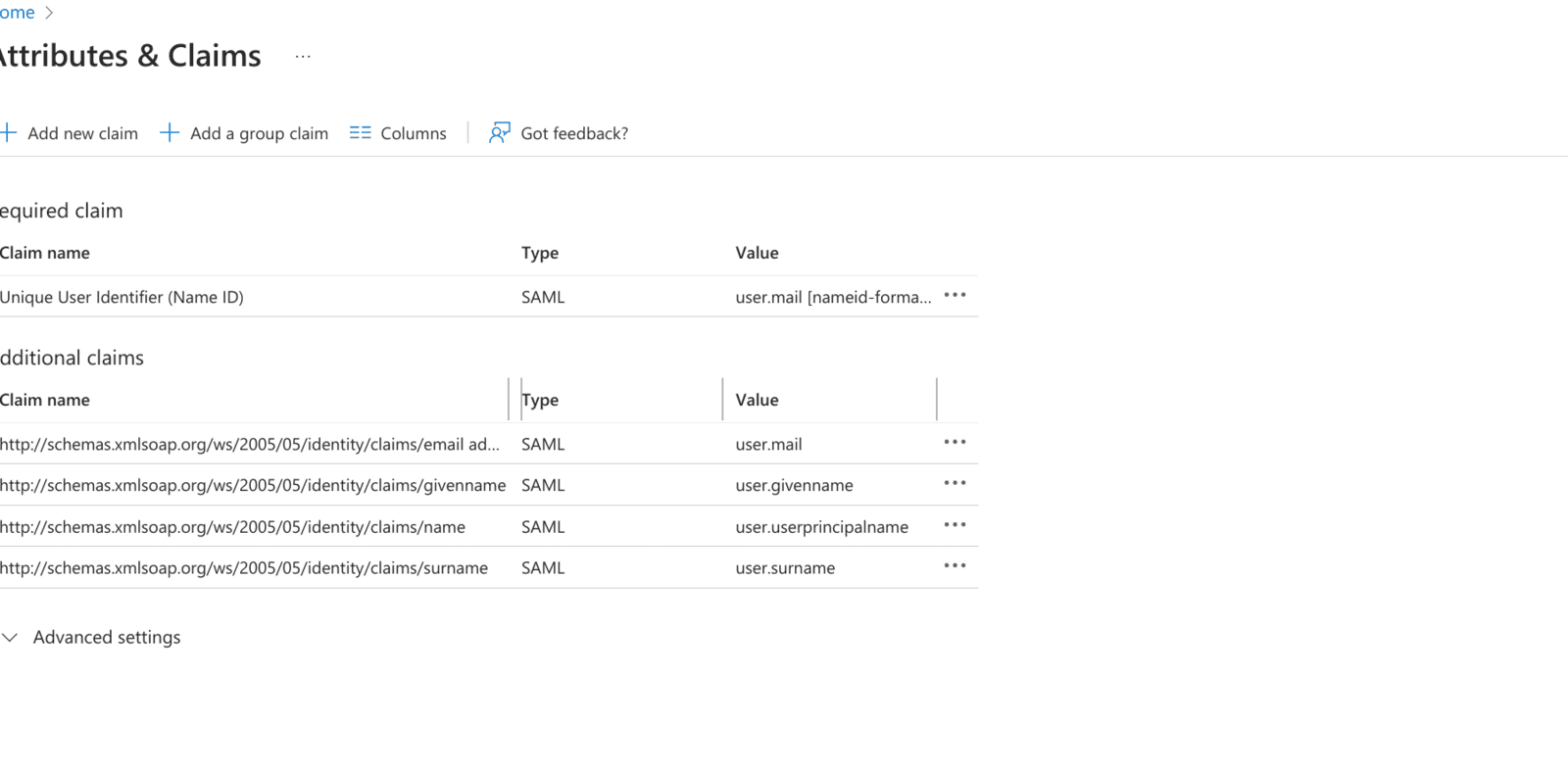
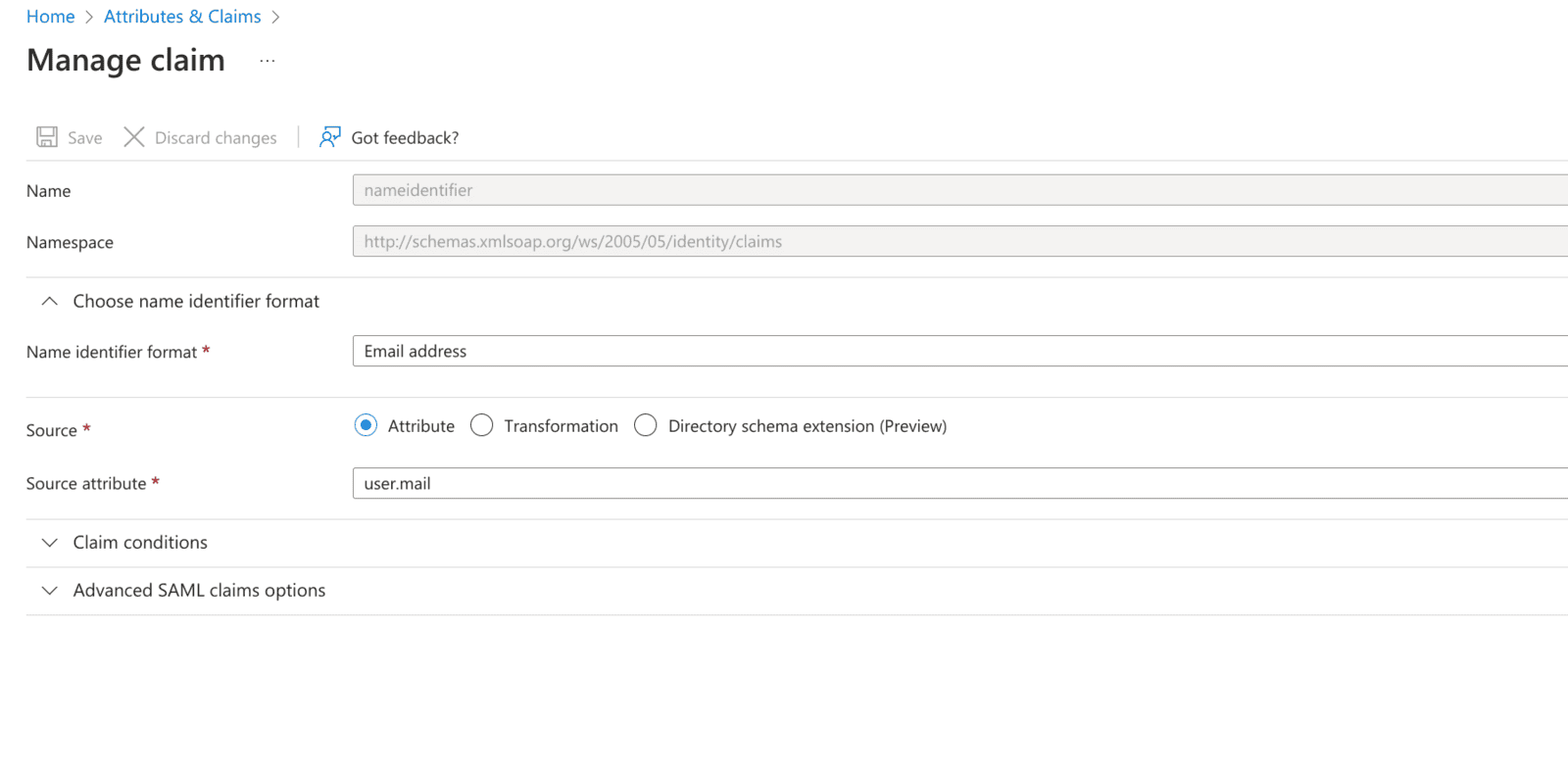
10. Under User Attributes, change User Identifier to user.mail
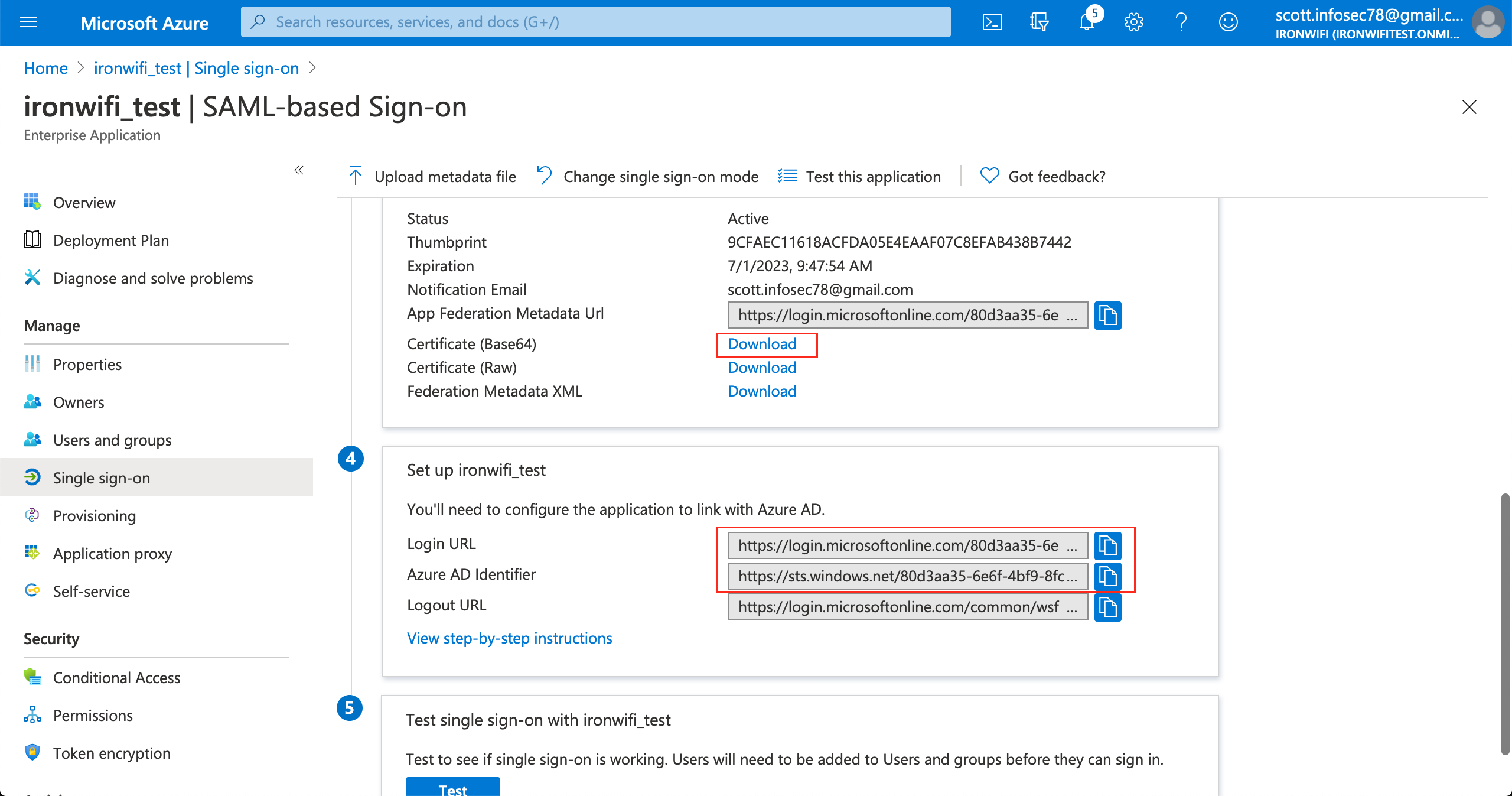
11. Scroll down on the single sign on page, click on "Set up your_application_name"
12. Copy SAML Single Sign-On Login URL value
13. Copy SAML Azure AD Identifier(Entity ID) value
.png)
14. copy SAML Signing Certificate - Base64 encoded content
.png)
Sign in to IronWiFi Console
1. Click on Networks > Captive Portals
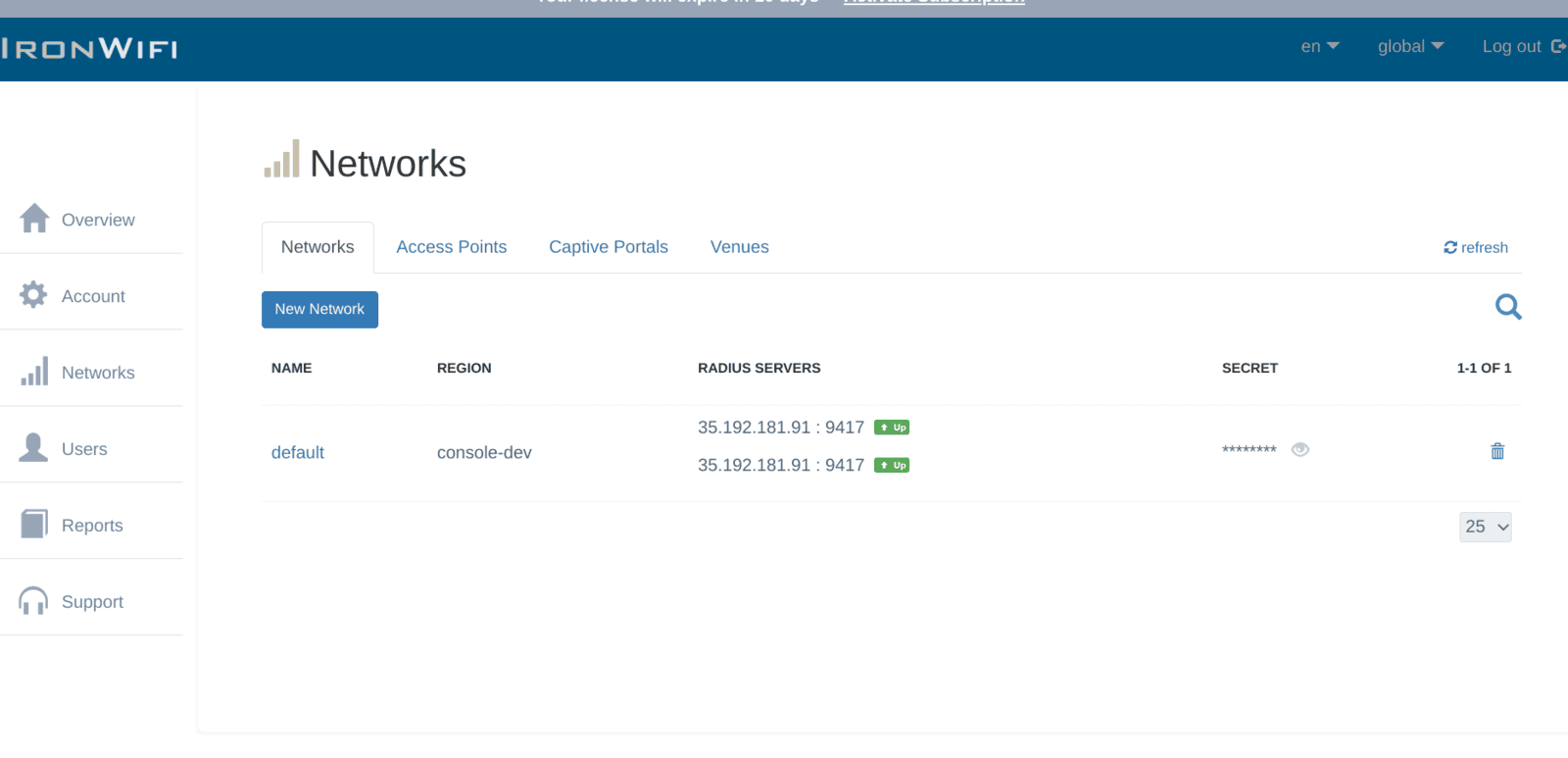
2. Create New Captive Portal
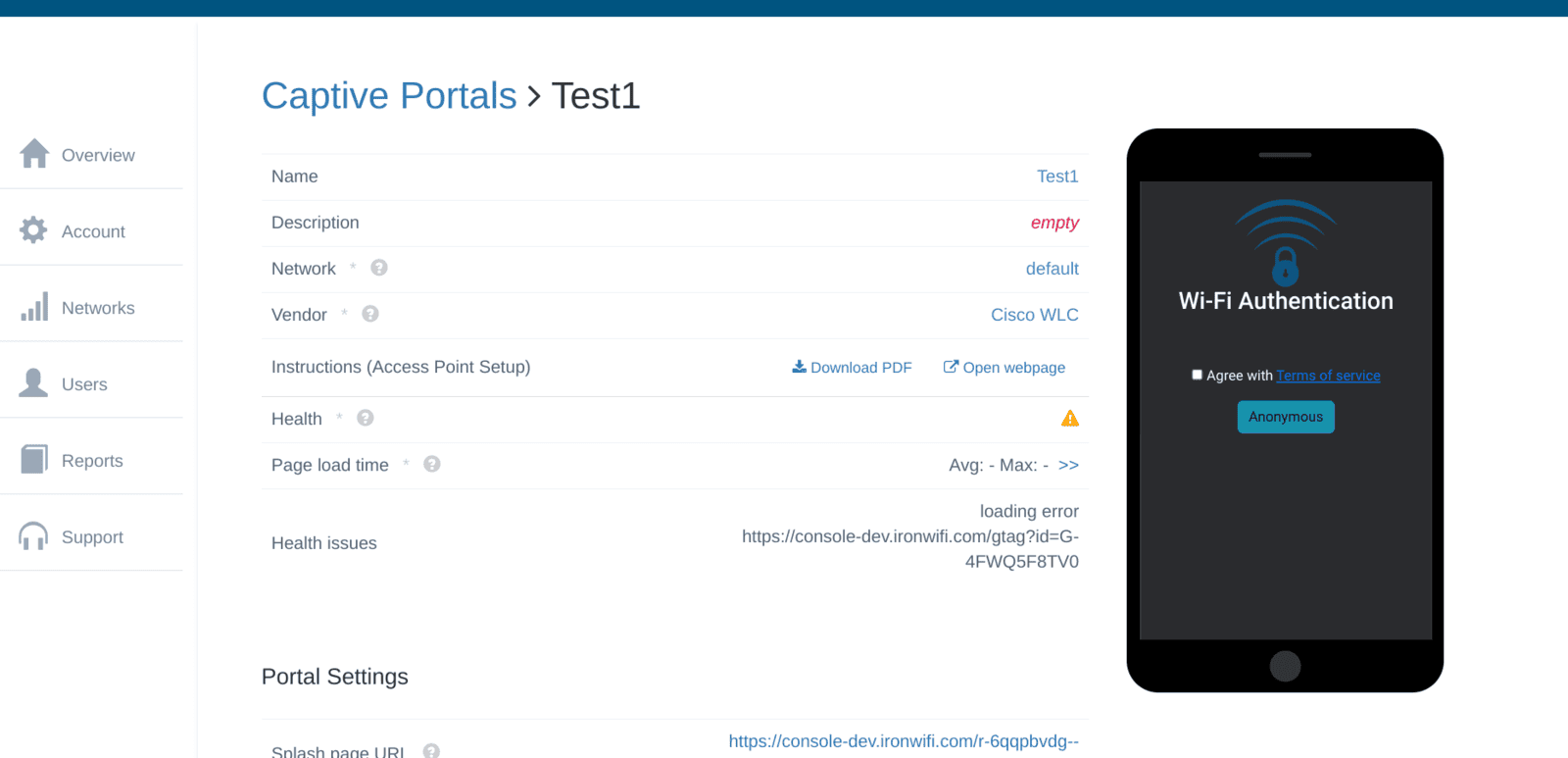
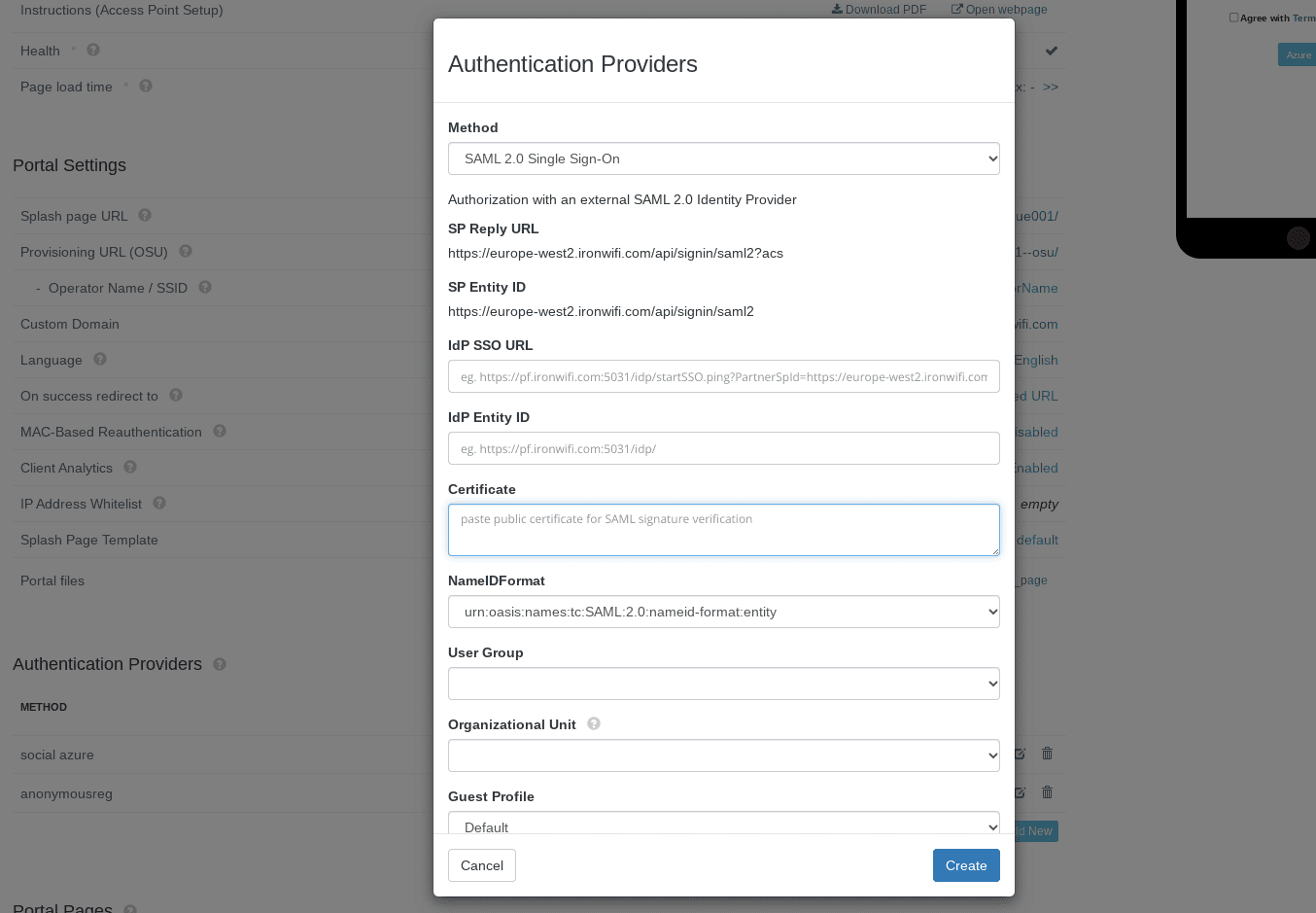
3. Expand the Authentication Providers menu and click Add New
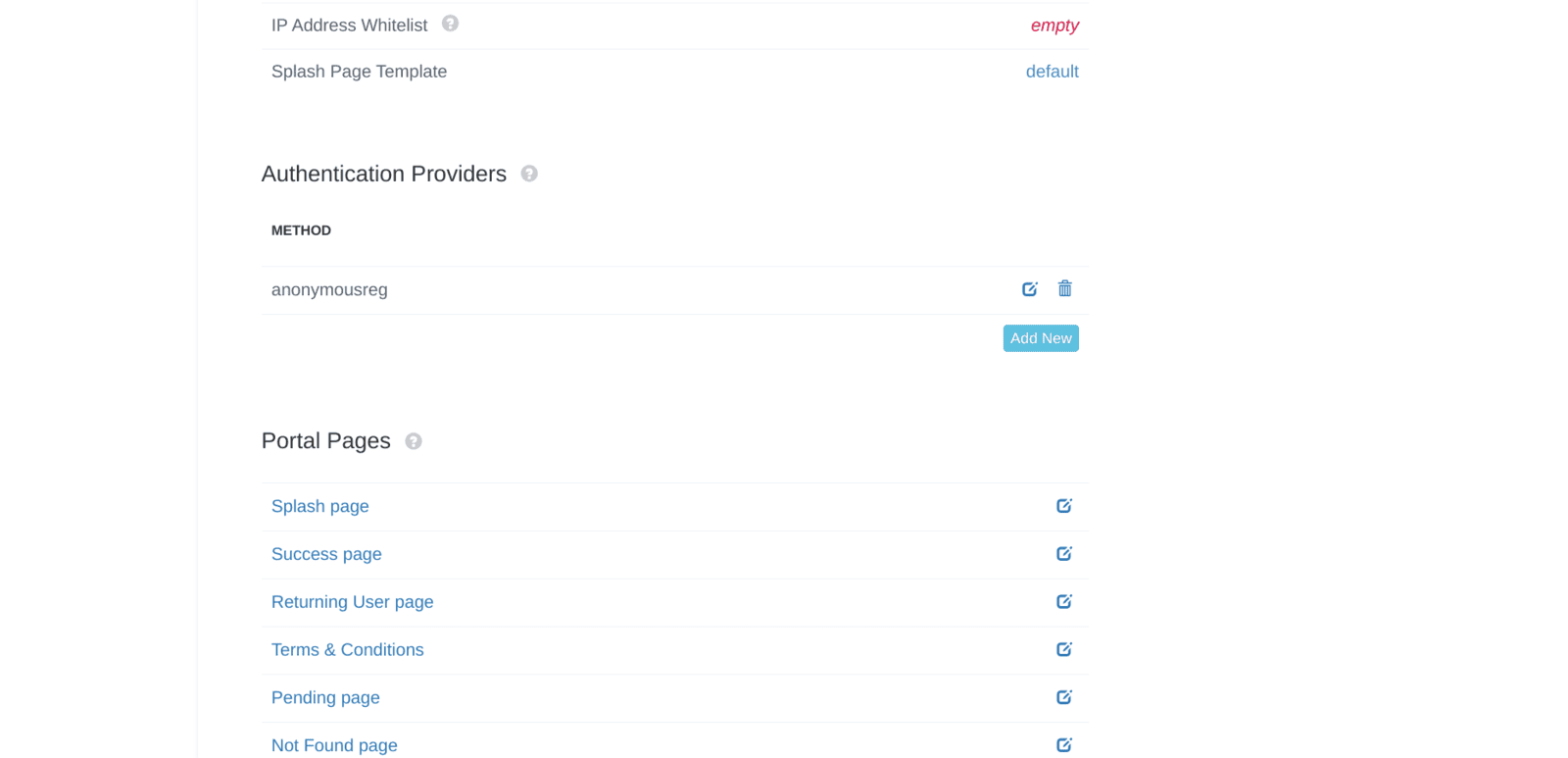
4. select SAML2 Single Sign-on method
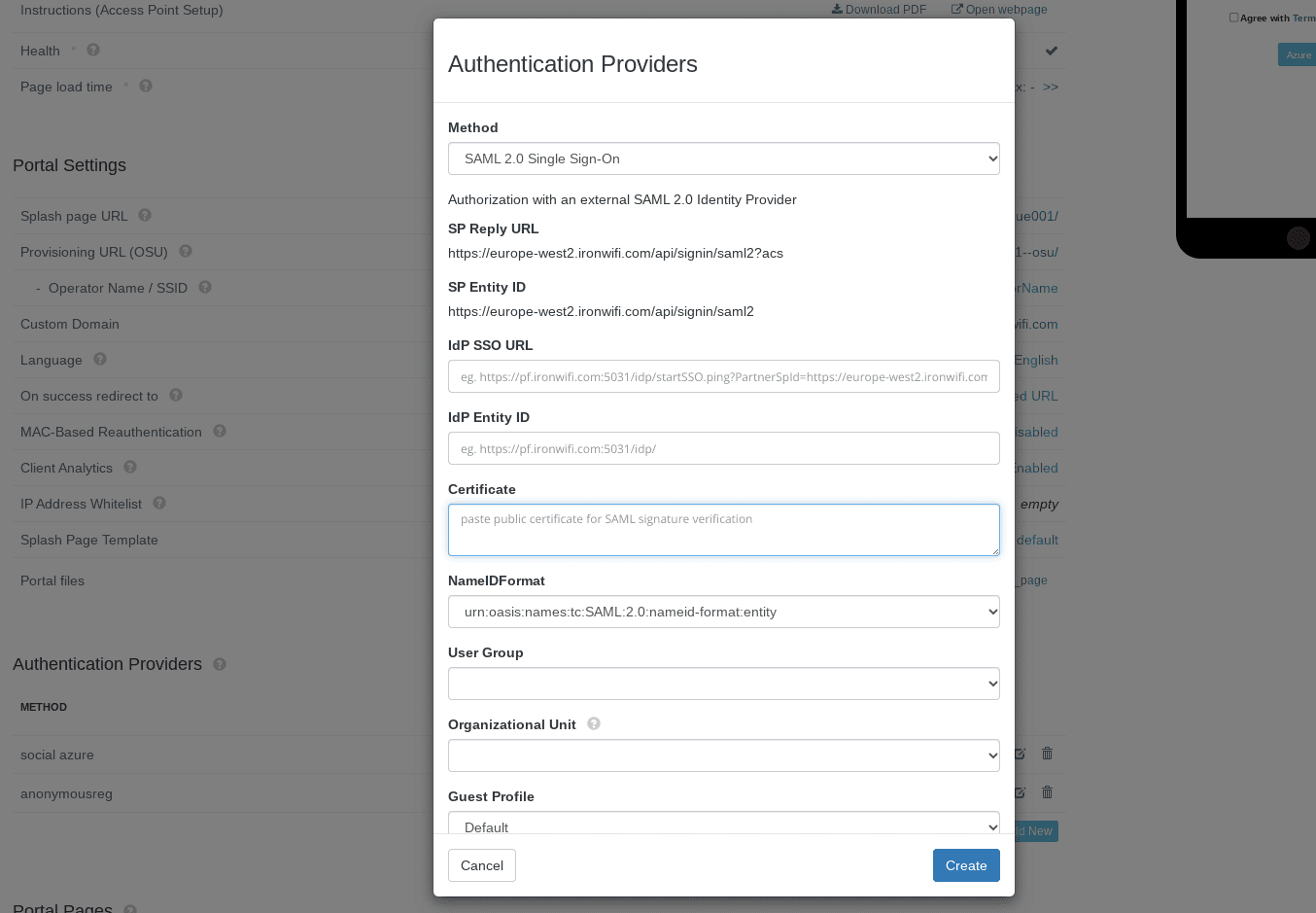
5. Paste copied SAML Single Sign-On Login URL value to SSO URL
6. Paste copied SAML Entity ID(Azure AD Identifier) value to IDP Entity ID
7. Paste copied SAML Signing Certificate - Base64 encoded content to Certificate
8. Select NameIDFormat value urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
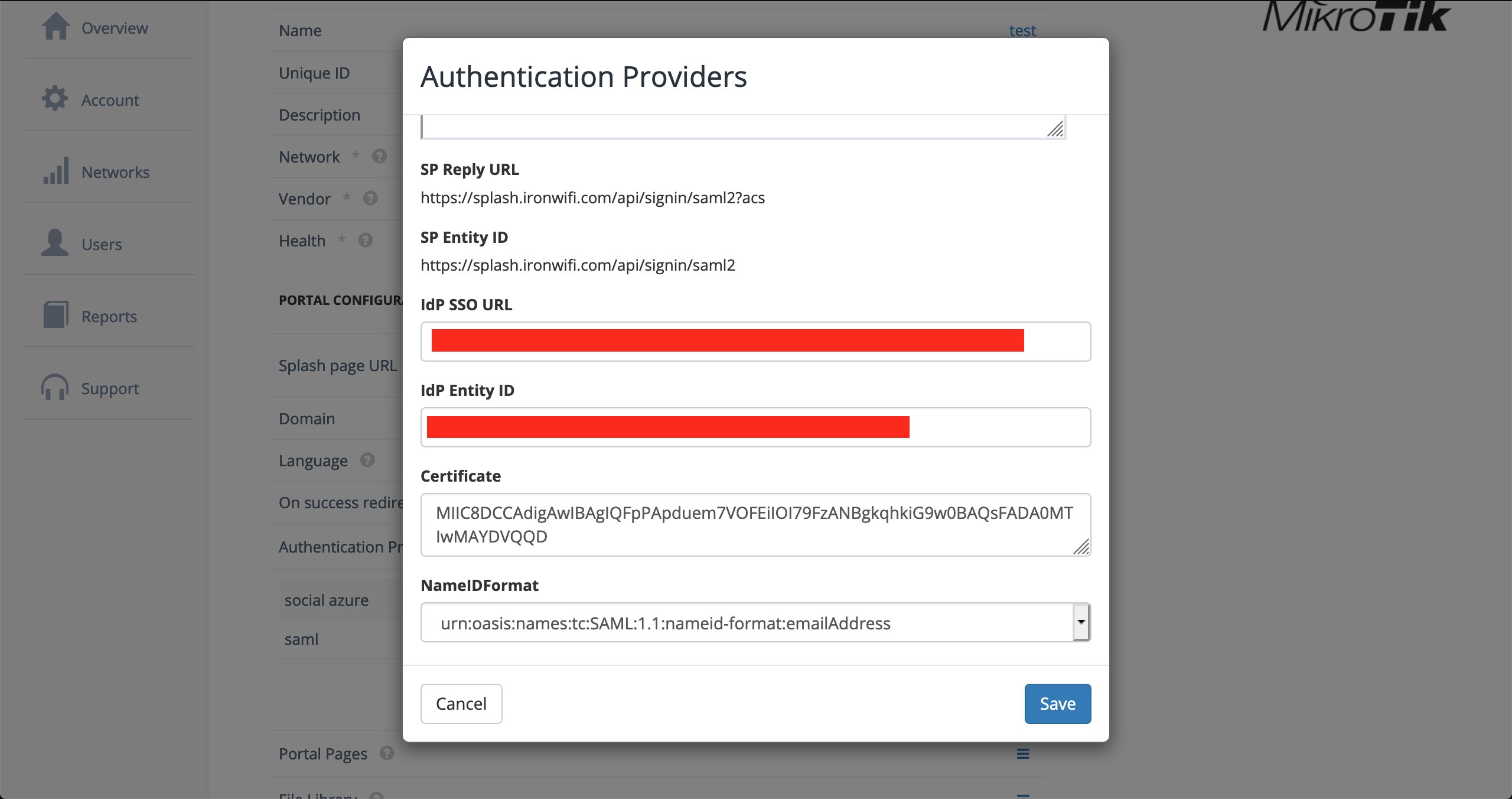
9. Click Save
- *.msauth.net
login.live.com
aadcdn.msftauth.net
*.logincdn.msftauth.net
*.microsoftonline-p.com
aadcdn.msauthimages.net
login.microsoftonline.com
*.aadcdn.msftauthimages.net
*.events.data.microsoft.com
*.aadcdn.microsoftonline-p.com
11. You can test your SAML authentication using Azure Active Directory
Related Articles
Azure
Our azure integrations allow you to import users from your Azure Active Directory, use Azure SAML authentication, set up 2FA and more. We provide instructions to help you get up and running as fast as possible, see the links below and follow the ...Okta (SAML)
This page explains the configuration of Okta (SAML) in conjunction with IronWiFi Captive Portal. OKTA Console Settings 1. Navigate to admin Okta console https://login.okta.com/ 2. Go to the Applications > Applications -> Browse App Catalog -> search ...Azure AD OAuth
This page provides instructions on how to configure your Azure Active Directory to allow Captive Portal authentication with OAuth. Navigate to https://portal.azure.com Go to Azure Active Directory submenu 3. Select the active directory you wish to ...Azure AD Connector
To manage your wireless users using Azure Active Directory account, you can enable remote synchronization with your Azure account for users in specific groups. Log in to the Azure Portal From the main menu, navigate to Azure Active Directory > ...Azure AD Authentication with PEAP-MSCHAPv2
This tutorial provides instructions on how to make PEAP-MSCHAPv2 authentication work with IronWiFi and Azure AD Domain Services. enable Azure AD Connector enable Azure AD Domain Services create CentOS virtual machine Make sure to choose the same ...